 (37)
(37)
 (25)
(25)
Autorías: Hadeer Idan Ghanim, Ishraq Mahmood. Localización: Revista iberoamericana de psicología del ejercicio y el deporte. Nº. 3, 2021. Artículo de Revista en Dialnet.
The melting duration in the photovoltaic/phase-change material (PV/PCM) system is a crucial parameter for thermal energy management such that its improvement can realize better energy management in respect to thermal storage capabilities, thermal conditions, and the lifespan of PV modules. An innovative and efficient technique for improving the melting duration is the inclusion of an exterior metal foam layer in the PV/PCM system. For detailed investigations of utilizing different metal foam configurations in terms of their convective heat transfer coefficients, the present paper proposes a newly developed mathematical model for the PV/PCM–metal foam assembly that can readily be implemented with a wide range of operating condition
... Show More (40)
(40)
 (40)
(40)
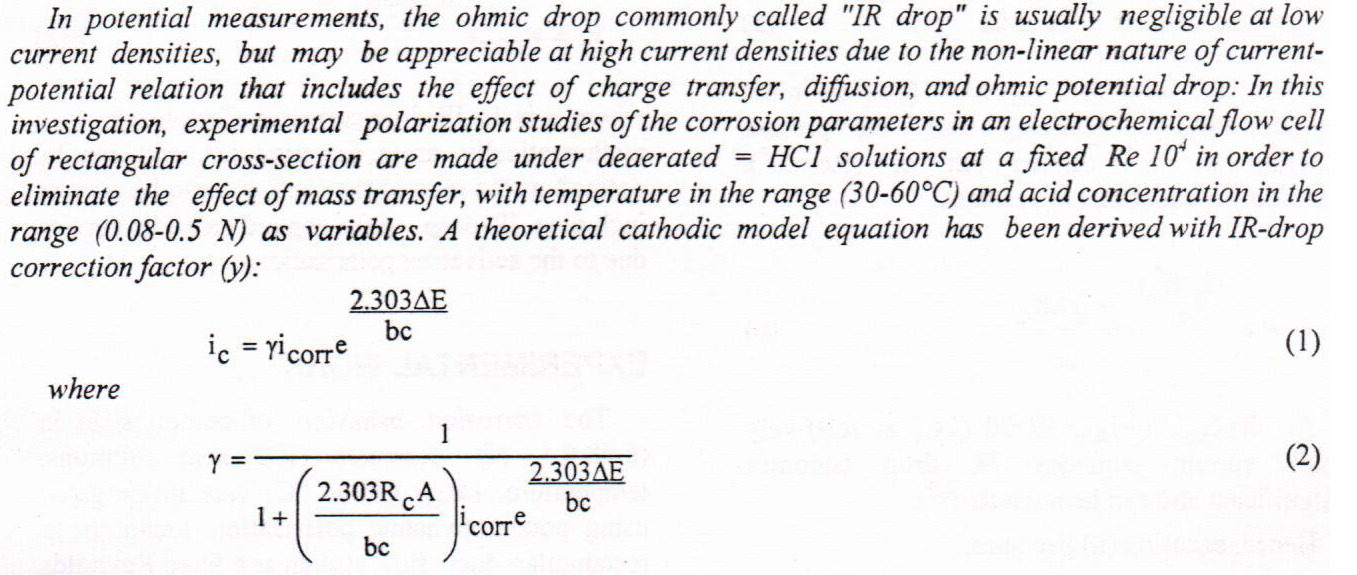
The experimental and theoretical methods were studied for inhibition of the corrosion titanium in HCl by using neomycin sulfate drug. The results of neomycin sulfate drug had good corrosion protection for titanium in hydrochloric acid and the inhibition efficiency (%IE) increasing with increasing concentration of drug because the neomycin sulfate drug had adsorption from acid solution on surface of titanium metal. The program of hyperchem-8.07 was used for theoretical study of the drug by molecular mechanics and semi-empirical calculations. Quantum chemical was studied drug absorption and electron transferred from the drug to the Titanium metal, also inhibition potentials of drug attachment with the (LUMO-HOMO) energy gap,
... Show More (5)
(5)
This paper presents a computer simulation model of a thermally activated roof (TAR) to cool a room using cool water from a wet cooling tower. Modeling was achieved using a simplified 1-D resistance-capacitance thermal network (RC model) for an infinite slab. Heat transfer from the cooling pipe network was treated as 2-D heat flow. Only a limited number of nodes were required to obtain reliable results. The use of 6th order RC-thermal model produced a set of ordinary differential equations that were solved using MATLAB - R2012a. The computer program was written to cover all possible initial conditions, material properties, TAR system geometry and hourly solar radiation. The cool water supply was considered time
... Show MoreStenography is the art of hiding the very presence of communication by embedding secret message into innocuous looking cover document, such as digital image, videos, sound files, and other computer files that contain perceptually irrelevant or redundant information as covers or carriers to hide secret messages.
In this paper, a new Least Significant Bit (LSB) nonsequential embedding technique in wave audio files is introduced. To support the immunity of proposed hiding system, and in order to recover some weak aspect inherent with the pure implementation of stego-systems, some auxiliary processes were suggested and investigated including the use of hidden text jumping process and stream ciphering algorithm. Besides, the suggested
... Show MoreThe primary objective of this paper is to improve a biometric authentication and classification model using the ear as a distinct part of the face since it is unchanged with time and unaffected by facial expressions. The proposed model is a new scenario for enhancing ear recognition accuracy via modifying the AdaBoost algorithm to optimize adaptive learning. To overcome the limitation of image illumination, occlusion, and problems of image registration, the Scale-invariant feature transform technique was used to extract features. Various consecutive phases were used to improve classification accuracy. These phases are image acquisition, preprocessing, filtering, smoothing, and feature extraction. To assess the proposed
... Show More (2)
(2)
This study proposed a biometric-based digital signature scheme proposed for facial recognition. The scheme is designed and built to verify the person’s identity during a registration process and retrieve their public and private keys stored in the database. The RSA algorithm has been used as asymmetric encryption method to encrypt hashes generated for digital documents. It uses the hash function (SHA-256) to generate digital signatures. In this study, local binary patterns histograms (LBPH) were used for facial recognition. The facial recognition method was evaluated on ORL faces retrieved from the database of Cambridge University. From the analysis, the LBPH algorithm achieved 97.5% accuracy; the real-time testing was done on thirty subj
... Show More (9)
(9)
 (2)
(2)
